- /
- Storage Guides
- /
- Immutability
- /
- Immutable Backups and Their Role in Data Resiliency
Immutable Backups and Their Role in Data Resiliency
ESG, a leading IT research firm, recently surveyed IT leaders worldwide to assess how prepared their backup storage environments are to face the growing ransomware threat.
The findings were shocking: two-thirds of organizations were hit in the last two years, and most attacks targeted backups, aiming to make recovery impossible and force ransom payments.
This is why forward-thinking organizations are turning to immutable backups. By making backup data physically unalterable for a defined retention period, immutability ensures that you always have a clean, trusted recovery path when ransomware strikes.
In this article, you'll learn what immutable backups are, why they matter now more than ever, and how to implement them effectively to build ransomware-proof resilience into your backup strategy.
Key Takeaways
- Immutable backups are ransomware-proof by design. With WORM policies, immutability locks data at the storage layer, making it physically unalterable—even with stolen admin credentials.
- Cyber resilience depends on storage, not just software. “Delete protection” flags and admin controls can be bypassed. Only storage-enforced immutability guarantees that retention locks will hold until they expire.
- Backups are now ransomware’s primary target. In most attacks, hackers go after recovery data first. Immutable backups eliminate this risk by ensuring recovery points cannot be encrypted, deleted, or silently corrupted.
- Ootbi (Out-of-the-Box Immutability) delivers immutability purpose-built for Veeam. Ootbi integrates immutability at the storage layer, enforces Zero Trust principles, and simplifies management for lean IT teams.
What Is an Immutable Backup?
An immutable backup is a backup copy that cannot be modified, deleted, or encrypted for the duration of its retention window. This means no one—not even a privileged admin or a fully compromised attacker—can alter or erase that backup data.
This immutability is enforced at the storage level through mechanisms like S3 Object Lock in Write Once, Read Many (WORM) mode. Unlike permission-based “read-only” flags that can still be bypassed, storage-native immutability ensures data is physically and logically locked until its retention policy expires.
In practice, immutable backups guarantee that every restore point is a trustworthy, untampered copy of history, giving your organization a clean path to recovery when every other safeguard fails.
Do Immutable Backups Protect Against Ransomware?
Studies show that in 96% of ransomware attacks, backup data is the primary target, corrupted or deleted before production systems are encrypted. If that happens, recovery is gone.
At the same time, 81% of IT leaders agree that immutable backup storage is the best way to protect against ransomware. Why? Because it makes recovery data untouchable—even if attackers gain full administrative control.
That's why immutability is known as the last line of defense against ransomware, allowing smooth ransomware recovery when everything else is compromised.
Here's how immutable backups stop ransomware tactics:
- Storage-enforced locking: Data is protected at the storage layer, not by software permissions, so even domain admins or hijacked service accounts can't alter it.
- Credential-proof protection: Stolen or elevated credentials can't bypass data immutability—retention rules are hardwired until expiration.
- Write-once integrity: WORM policies prevent ransomware from overwriting clean restore points with corrupted or encrypted data.
- Guaranteed recovery path: Every immutable backup is a verifiable snapshot of history, ensuring recovery data stays clean, consistent, and accessible.
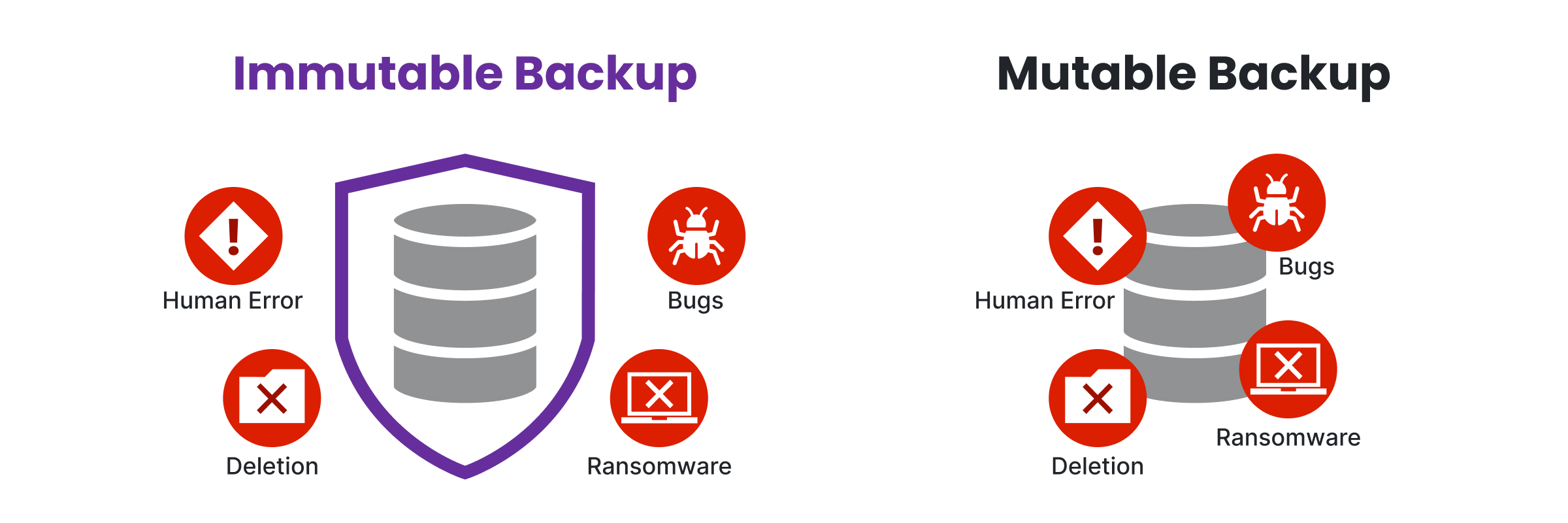
Immutable Backup vs. Traditional (Mutable) Backup
The main difference between mutable and immutable backups is that one delivers true ransomware resilience, while the other remains vulnerable to increasingly sophisticated attacks.
- Mutable backups depend on permissions and trust models, which ransomware routinely bypasses to corrupt or delete recovery data.
- Immutable backups, on the other hand, eliminate this weakness entirely by enforcing storage-level rules that ransomware cannot alter, even with stolen credentials.
To better illustrate the gap in data protection, here are the fundamental mechanics behind each backup strategy:
| Aspect | Traditional (Mutable) Backup | Immutable Backup |
|---|---|---|
| Data Control | Governed by software permissions, ACLs, or admin credentials | Enforced at storage level—data cannot be modified or deleted until retention expires |
| Vulnerability to Ransomware | High: ransomware can encrypt or delete backup files once it compromises admin access | None: ransomware cannot alter, encrypt, or erase data under immutability rules |
| Risk of Insider Threats | Elevated: privileged users or malicious insiders can tamper with or remove backups | Neutralized: even privileged accounts cannot override immutability policies |
| Silent Corruption | Possible: old restore points can be silently overwritten or replaced with bad data | Impossible: WORM rules ensure each restore point remains intact for its full retention period |
| Recovery Reliability | Uncertain: restores must be verified to ensure data wasn’t tampered with | Guaranteed: every restore point is a verified snapshot of clean history |
| Compliance & Auditability | Dependent on access logs and controls that can be manipulated | Creates a cryptographically verifiable, unalterable audit trail — meets HIPAA, GDPR, and NIS2 standards |
| Operational Overhead | Requires frequent monitoring, testing, and manual verification of backup integrity | Minimal: immutability enforces protection automatically at the storage layer |
| Cost vs. Risk Tradeoff | Lower upfront cost, but exposes organizations to catastrophic ransomware downtime | Slightly higher storage cost, but mitigates multimillion-dollar business losses |
The Main Benefits of Immutable Backups
- Cyberattack-proof protection: Immutability blocks not just ransomware but also malware, insider sabotage, and supply-chain exploits by locking data at the storage layer, beyond the reach of stolen credentials or rogue scripts.
- Resilience against human error: Deletions, misconfigured jobs, or accidental wipes can’t erase immutable backups—once written, recovery points remain intact until their retention window expires.
- Faster, more reliable recovery: Because immutable restore points can’t be tampered with, IT teams skip lengthy integrity checks and recover immediately from clean, verified data—cutting downtime from days to hours.
- Regulatory and long-term retention: Frameworks like HIPAA, GDPR, and NIS2 demand non-rewritable, non-erasable storage; immutability enforces this by design while also preserving archives for audits, legal holds, and business continuity.
- Forensic-grade audit trails: Immutable backups create a verifiable chain of custody, capturing exactly when data was written and ensuring it hasn’t changed—critical for breach investigations, root-cause analysis, and legal defense.
- Reduced financial exposure: By neutralizing ransomware and ensuring fast recovery, immutability slashes downtime costs, avoids ransom payments, and can even lower cyber insurance premiums.
- Proven data integrity: With cryptographic hashing and WORM enforcement, every immutable backup is a verifiable snapshot of history, guaranteeing that restore points are clean, consistent, and uncompromised.
How to Implement Immutable Backups: A Step-by-Step Approach
If done right, implementing immutability will transform your backups from “probably safe” into truly resilient. If done wrong, it’s just another false sense of data security.
Here’s the step-by-step playbook for implementing an immutable backup solution, ensuring it stays untouchable no matter what attackers throw at it.
Step 1: Establish a Resilient Backup Strategy
Every strong immutability plan starts with the basics. If your backup architecture is weak, immutability won’t save you. It’ll just lock in bad habits.
That’s why the 3-2-1-1-0 rule is the foundation for everything, involving:
- 3 copies of your data
- 2 different storage mediums
- 1 copy offsite
- 1 immutable or air-gapped copy
- 0 backup verification errors
Follow this, and you’ve already eliminated most single points of failure. Ignore it, and no amount of “immutable” storage will make up for the cracks.

Step 2: Choose the Right Immutable-Capable Storage
Immutability lives (or dies) at the storage layer. If your platform can't enforce true WORM (Write Once, Read Many) policies, then "delete protection" is just security theater.
Here are the main ways organizations achieve it today:
- Object storage with S3 Object Lock (AWS S3, on-prem S3-compatible systems like Object First's Ootbi) delivers native immutability with flexible retention locks that fit modern backup workflows.
- WORM media like tape remains a cost-effective archival option, but retrieval speed and operational overhead make it less practical for fast recovery.
- Vendor-secured repositories (such as hardened Linux repos in Veeam environments) offer immutability at the OS level, though they demand airtight privilege separation to prevent admin misuse.
When evaluating, don't just ask "does it support immutability?" Ask where and how the lock is enforced. If it isn't happening at the storage layer itself, you're building on sand.
Step 3: Define and Enforce Retention Policies
Immutability without smart retention planning is like a vault with open doors. It looks secure until you actually need it.
To make immutability meaningful, you need precise, enforceable policies that align with your organization's realities.
Here's what to anchor them to:
- Compliance mandates (HIPAA, GDPR, NIS2, SEC, etc.)
- Business RTO/RPO objectives (how much data you can afford to lose vs. how quickly you must recover)
- Archival needs (legal holds, historical analysis, long-term continuity)
Lock those rules in with retention locks such as governance mode for admin-driven control and compliance mode for regulator-level assurance.
Either way, the result is the same: no privileged account, rogue script, or misstep can erase protected data before its time.
Step 4: Harden Access and Privilege Separation
Immutability locks data at the storage layer, but if access controls are sloppy, attackers will just walk in through the front door.
The key is to build strict privilege boundaries so that no single account or compromise can break the protection chain.
To do it right you need:
- Role-based access control (RBAC) keeps backup admins, storage admins, and security admins in separate lanes.
- MFA and PAM (Privileged Access Management) ensure that a stolen password alone can't delete or modify backups.
- Segmentation isolates backup systems from production domains so a domain controller breach can't cascade downstream.
RBAC, MFA, and segmentation are like guards, and without them, you're trusting luck instead of security.
Step 5: Implement Offsite Copies and Air Gaps
Immutability alone isn’t enough if your backups live in the same blast radius as production.
True data resilience comes from isolation, which prevents attackers (or disasters) from reaching every copy at once.
Building that safety net involves:
- Cloud-based immutable tiers to provide both geographic and network isolation.
- Air-gapped systems, such as tape or offline repositories, cut off malware entirely by removing the attack surface.
- Delayed deletions create a final buffer if someone tampers with retention settings, data lingers long enough to recover.
Redundancy across environments (object storage on-prem) ensures that no single failure, breach, or disaster wipes you out, being a difference between having backups and having survivable backups.
Step 6: Automate Verification and Monitoring
An immutable backup that isn’t tested is just a comforting illusion. You don’t want to discover corruption, misconfigurations, or missed retention locks in the middle of an outage.
That’s why verification must be relentless and automated.
- Integrity checks: hash-based validation ensures every block of data is exactly as it was when written.
- Regular test restores: prove that your RTO/RPO targets aren’t just numbers on a slide—they actually work under fire.
- Ransomware detection: catches red flags early, from unexpected deletions to unusual access attempts or abnormal change rates.
This turns immutability from a promise into a guarantee, because if you can’t prove your backups are ready, they’re not.
Step 7: Validate Through Real-World Testing
Paper policies and checkboxes don’t stop breaches—pressure-testing does. Don’t just trust that immutability is working, try to break it.
- Deletion attempts: verify that retention locks hold, even when using privileged accounts.
- Red-team exercises: simulate insider abuse or malware attempting to corrupt backups.
- Failure-point testing: push your system until it fails, then close the gaps you find.
The organizations that test ruthlessly are the ones that recover when others collapse.
Ootbi: The Best Storage to Implement Immutable Backups for Veeam
Immutable backups are only as resilient as the storage they live on. If the underlying platform can be bypassed, misconfigured, or exploited, immutability is just a label, not real protection.
That's why we created Ootbi (Out-of-the-Box Immutability), which delivers secure, simple, and powerful on-premises backup storage for Veeam customers.
Ootbi is secure by design as defined by CISA. It was built around the latest Zero Trust Data Resilience principles, which follow an "Assume Breach" mindset that accepts individuals, devices, and services attempting to access company resources are compromised and should not be trusted.
Download the white paper and learn why Ootbi is the Best Storage for Veeam.
How Hans Hundegger AG Implemented Immutable Backups with Ootbi
Hans Hundegger AG, a global leader in CNC joinery machines, faced an aging backup infrastructure that couldn’t keep pace with modern security and performance demands. With a lean IT team and rising support tickets, they needed stronger ransomware protection and simpler management.
By partnering with Erik Sterck GmbH, they deployed Object First’s Ootbi appliance, which was selected for its storage-level immutability, ensuring maximum protection against ransomware.
The results were dramatic:
- Immutable storage provided security against ransomware threats
- Automated restore guaranteed backups take place and are easily recoverable in case of disaster
- The average restore time dropped 66%, from six hours to two
- Seamless integration with Veeam architecture significantly reduced administrative overhead
Read the full case study to see how Hans Hundegger AG strengthened security and accelerated recovery with Ootbi by Object First.
Summary
Immutable backups have become the last line of defense against ransomware, but they only work if they’re implemented correctly. By locking data at the storage layer with WORM policies, offsite data backup isolation, and continuous verification, organizations can guarantee clean recovery points that no attacker can touch.
The payoff is enormous: faster restores, resilience against insider threats, ransomware attacks, human error, and the confidence that compliance requirements are met. And with purpose-built solutions like Ootbi by Object First for Veeam, immutability isn’t just theory but a practical, scalable, and proven in the real world.
FAQ
What is an Indelible Backup?
An indelible backup is the same as an immutable backup: once written, data cannot be modified, deleted, or overwritten. Some vendors market “indelible” as a differentiator, but industry-standard terminology is immutable backup.
What’s the Difference Between Air-Gapped and Immutable Backup?
Air-gapped backups are physically disconnected from networks, cutting off malware access but creating complexity in restores. Immutable backups remain online yet unchangeable at the secure data storage layer, combining security with fast recovery and better integration with modern workflows.
What Is the Recommended Frequency for Updating Immutable Backups?
Backup frequency should match how often critical data changes and align with RPO (Recovery Point Objective). Regular verification is essential to confirm new restore points are intact and usable.
Why Do Immutable Backups Matter Now More Than Ever?
Because ransomware now specifically targets backup systems, 96% of attacks go after recovery data first. Immutable backups remove this attack surface entirely by making backups physically unalterable, even with stolen admin credentials. This approach is essential for achieving ransomware resilience.
What Is the Immutability Period and Why Does It Matter?
The immutability period is the locked time window during which data cannot be changed or deleted. Setting it correctly is critical: too short leaves gaps for ransomware to exploit, while too long can inflate storage costs and limit flexibility.