Data protection does not end when backups expire, or hardware reaches the end of its life. Even after files are deleted, or a disk is reformatted, sensitive information can linger in ways that make it recoverable to anyone with the right tools and motivation. This is a well‑documented issue across multiple security authorities: Columbia University notes that deleting the contents of a disk “normally does not actually erase the file contents,” and CISA warns that even after deletion or reformatting, “the file is probably still somewhere on your machine.”
That’s why Object First is introducing a secure erase feature across all Object First appliances with 1.7 Update 3.
Secure erase is not something most customers will use every day. It's for appliance end-of-life operations: returning hardware, supporting operations, and meeting strict compliance requirements. That said, for those utilizing the Object First Consumption model, you’ll rely on these steps whenever you scale up to a bigger appliance. This feature closes the loop on data lifecycle security and reinforces Object First’s commitment to delivering secure, simple, powerful data protection for your Veeam environments.
What is secure erase?
Deletion, reformatting, or factory resets do not reliably remove sensitive data. True sanitization requires specialized methods that eliminate recoverable remnants.
Secure erase is a process that renders data unrecoverable, even with advanced forensic techniques. NIST SP 800‑88R2, the NIST Guidelines for Media Sanitization, defines sanitization as a process that “renders access to target data on the media infeasible for a given level of effort.” This framework outlines two primary approaches used across the industry:
- Overwrite, which replaces existing data across the entire disk surface.
- Cryptographic erase, which invalidates the encryption keys protecting the data, making the underlying information unreadable.
In the backup data storage industry, secure erase serves a very specific purpose: it is used only when hardware is being decommissioned, returned, or repurposed—never during normal operations. When hardware is ready to leave your hands, secure erase ensures that no residual data remains on the disks.
Sanitation and disposition decision flow
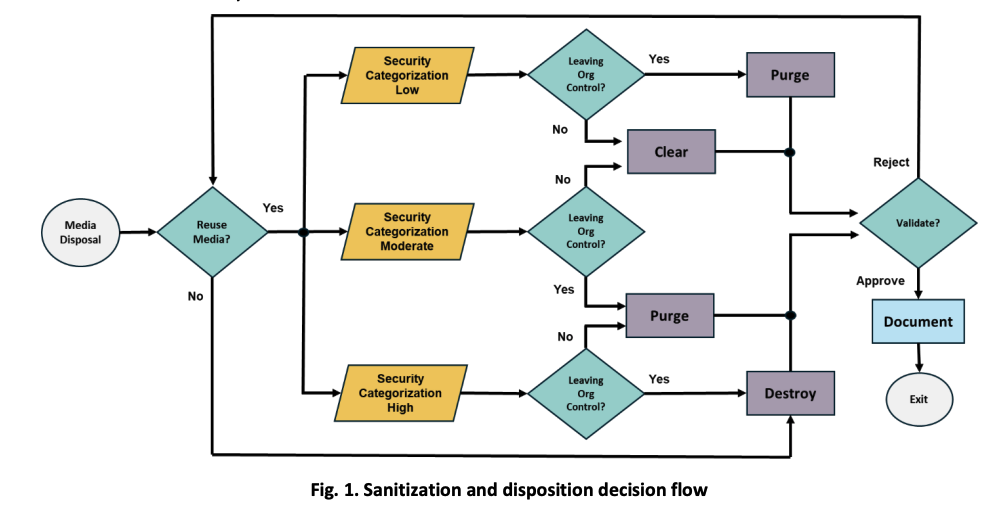
Image courtesy of NIST SP 800‑88 Revision 2 (2025), page 20.
The above NIST decision flow shows how to choose the appropriate method for wiping storage media based on data sensitivity and whether the device will remain within the organization. First, you identify the data’s sensitivity level. Then you decide if the hardware will be reused internally or sent somewhere else. Those two factors determine whether you should clear, purge, or destroy the media. NIST also notes that not every device supports every sanitization method, and organizations may accept some risk when dealing with moderately sensitive data. After choosing a method, the final steps are to verify that the secure erase procedure was successful and subsequently record what was done for auditing and compliance.
Why secure erase matters in backup data storage
While secure erase protects data when hardware leaves customer control, it is only one layer of a broader defense‑in‑depth strategy. Veeam job‑level encryption ensures that even if data were exposed during service events or media handling, it would remain unreadable. Secure erase then provides the final guarantee that no recoverable data persists once the hardware is decommissioned or returned.
Compliance and regulatory pressure
Several major regulations require organizations to securely remove data from storage media before hardware is reused, returned, or decommissioned.
GDPR mandates the secure deletion of personal data under Articles 5(1)(e), 5(1)(f), and 32, which collectively requires organizations to prevent unauthorized disclosure—including during hardware disposal. HIPAA’s Security Rule (45 CFR §164.310(d)(2)) explicitly requires the removal of ePHI from electronic media before reuse.
PCI DSS v4.0 requires organizations to render cardholder data unrecoverable when deleted. Additional frameworks such as the Gramm‑Leach‑Bliley Act (GLBA), Sarbanes‑Oxley Act (SOX), and Family Educational Rights and Privacy Act (FERPA) all impose obligations to protect sensitive data throughout its lifecycle, including during disposal:
- SOX: Requires strong internal controls to prevent unauthorized access to financial data. Failing to securely wipe or dispose of data‑bearing hardware is treated as a breakdown of those controls.
- GLBA: Mandates that financial institutions safeguard customer information. FTC guidance under the Safeguards Rule explicitly requires secure wiping or destruction of storage media before disposal.
- FERPA: Requires educational institutions to protect student records, including ensuring that data is securely removed from devices before they are repurposed, transferred, or discarded.
NIST SP 800‑88R2 provides the widely adopted technical standard for meeting these requirements through validated sanitization methods such as cryptographic erase and overwrite.
Operational scenarios where secure erase is needed
Secure erase is most used when hardware is returned after a demo or evaluation, during consumption‑based upgrades that require evacuating a node or replacing a disk, or at end‑of‑life decommissioning when the appliance leaves customer control. These transitions create natural points of exposure, and secure erase ensures no recoverable data remains on the disks.
Routine service operations introduce a second, often overlooked leakage risk: replacing failed or degraded media. Whether the component is a Hard Disk Drive (HDD), Solid‑State Drive (SSD), or NVMe flash module, each device may still contain sensitive backup data even after failure. In many environments, Return Merchandise Authorization (RMA) workflows require sending these drives back to the manufacturer. Veeam job‑level encryption helps ensure that any leaked data remains unreadable, and organizations with Digital Media Retention (DMR) or Keep Your Hard Drive (KYHD) agreements can retain or destroy failed media instead of returning it to the vendor.
How secure erase works in Object First Appliances
As it was designed with NIST SP 800‑88R2 in mind, Object First’s Secure Erase feature is secure, safe, and aligned with industry expectations for data disposition. During normal operations, immutability remains absolute—backup data cannot be altered or removed during its retention period. Secure erase becomes available only when hardware is intentionally decommissioned.
Prerequisites and disk erase modes available
Before the workflow begins, telemetry must be enabled, and nodes must contain no remaining user data. Depending on the underlying hardware, the system automatically selects one of three erase modes: Cryptographic Erase, which instantly invalidates the disk’s internal encryption key; Secure Erase, where the disk controller overwrites the entire device with a defined pattern; or External Erase, where the service application performs a full‑disk overwrite. All disks are processed in parallel to reduce total erasing time.
After the erase completes, Object First validates the operation by reading test blocks and confirming that their hashes differ from the original data. Then, the system generates statistics that include the date, disk serial number, erase method, and confirmation of completion.
How common is secure erase in the backup data storage industry?
Secure erase is not consistently implemented across the industry. Many vendors rely on manual processes or third‑party tools, and some cloud providers offer only logical deletion rather than hardware‑level sanitization. Few backup data storage vendors provide built‑in, standards‑aligned workflows. For Veeam users, this means that Object First is positioned ahead of competitors, particularly in compliance‑driven markets.
Zero Trust from cradle to grave
Secure erase reinforces Object First’s Zero Trust approach to data protection. Data remains absolutely immutable throughout its lifecycle, and once hardware is decommissioned, it becomes unrecoverable.
The feature also reflects Object First’s brand promise. It is secure, eliminating the risk of data exposure when the hardware leaves your hands. It is simple, eliminating the need for third-party vendors or complicated tools to wipe your appliance. And it is powerful, delivering cryptographic secure erase sanitization in a fraction of the time it takes a traditional overwrite.
With secure erase, Object First continues to lead the way in delivering the most secure, simple, and powerful backup data storage platform for Veeam.
